butler lies | seeing & being seen | face threats | traces & conflict | anonymity & identifiability | multicultural virtual organizations | attention management
Butler Lies: Deception in Text-Based Communication
People frequently find themselves in situations where they want to end a conversation prematurely, perhaps because the conversation is boring, or because another event or activity is more important. There are also times when it is desirable to avoid a conversation altogether, or to postpone it to a later time. We refer to behavior in these situations as “availability management” – that is, behavior that allows us to control when and how we interact with others. Availability management can be difficult in that people typically want to appear polite, even when they are doing something (such as leaving or avoiding a conversation) that could be perceived as rude. Examples of common availability management behaviors include setting one’s instant messenger status to “away” or “busy” to avoid conversations only with certain people. This project focuses on how people use various technologies to manage their availability, and how we can design novel systems to improve support for these behaviors.
Publications
- French, M., Smith, M. E., Birnholtz, J., and Hancock, J. T. (2015) “Is This How We (All) Do It?: Butler Lies and Ambiguity Through a Broader Lens” To appear in Proceedings of the ACM Conference on Human Factors in Computing Systems (CHI). Seoul, Korea, April 18–23, 2015. (received honorable mention best paper award) [PDF]
- Reynolds, L., French, M., Smith, M.E., Hancock, J., and Birnholtz, J. (2014) “Detecting Deception in Text Messaging: The Role of Context, Relationships, the Lie and the Liar,” Presented at the Conference of the International Communication Association (ICA), Seattle, WA, May 22–26. [PDF]
- Smith, M., Aljuhani, A., Birnholtz, J., Hancock, J., and Reynolds, R. (2014) “Visiting the ‘Lie-brary:’ Exploring Data Engagement as Participant Incentive,” demonstration presented at the ACM Conference on Computer-Supported Cooperative Work (CSCW), Baltimore, MD, February 14–19.
- Smith, M.E., Hancock, J., Reynolds, L., and Birnholtz, J. (2014) “Everyday Deception or A Few Prolific Liars? The Prevalence of Lies in Text Messaging,” Computers in Human Behavior. [PDF]
- Birnholtz, J., Reynolds, L., Smith, M.E. and Hancock, J. (2013) “‘Everyone Has to Do It:’ A Joint Action Approach to Managing Social Inattention,” Computers in Human Behavior 29 (6), pp. 2230–2238. [PDF]
- Reynolds, L., Smith, M., Birnholtz, J., and Hancock, J. (2013) “Butler Lies From Both Sides: Actions and Perceptions of Unavailability Management in Texting,” Proceedings of the ACM Conference on Computer Supported Cooperative Work, San Antonio, TX, February 23 – 27, pp. 769–778 (received honorable mention best paper award). [PDF]
- Smith, M.E., Birnholtz, J., Reynolds, L., and Hancock, J. (2013). People, Place and Time: The Daily Rhythms of Deception in Interpersonal Text Messaging. Paper presented at the Conference of the International Communication Association (ICA) [PDF]
- Birnholtz, J., Hancock, J., Smith, M., & Reynolds, L. (2012). Understanding unavailability in a world of constant connection. Interactions 19(5) 32-35.
- Birnholtz, J., Guillory, J., Hancock, J. T., & Bazarova, N. (2010). “on my way”: Deceptive Texting and Interpersonal Awareness Narratives. Proceedings of the ACM Conference on Computer Supported Cooperative Work, Savannah, GA, pp. 1-4.
- Hancock, J., Birnholtz, J., Bazarova, N., Guillory, J., Perlin, J., Amos, B. (2009) “Butler Lies: Awareness, Deception and Design,” Proceedings of the ACM Conference on Human Factors in Computing Systems (CHI 09), Boston, MA, April 4-9, pp. 517-526 (25% acceptance rate).
Seeing and Being Seen: Architecture, Visibility, and Social/Sexual Encounters Using Location-Aware Mobile Apps
There is an increasingly popular array of mobile apps that identify physically proximate (often at the level of “feet away”) strangers with similar interests, which help overcome challenges in identifying shared interests or goals of others. The users one sees at any given time depends on who else is logged on and where they physically are, meaning that an average distance of users one sees can change. Our current research in this space looks at how people use Grindr, one such location-aware app for men who have sex with men (MSM). Grindr use facilitates identification of other MSM, but users delicately balance their impression management within the app. People must reveal enough information to appear attractive to others, but they must do so in a quasi-public, local environment that may expose their experimental behavior to others they do not wish to share it with (such as existing friends or romantic partners, family, etc.). We are interviewing current users of the application who experience Grindr networks of various average distance to other users, as well as conducting analysis on profile data to explore questions of user goals, impression management, and contexts of use.
Publications:
- Fitzpatrick, C., Birnholtz, J., and Brubaker, J. (2015) “Social and Personal Disclosure in a Location-Based Real Time Dating App,” Proceedings of the 48th Annual Hawaii International Conference on System Science, Kauai, HI, January 5–8. [PDF]
- Birnholtz, J., Fitzpatrick, C., Handel, M., and Brubaker, J. (2014) “Identity, Identification and Identifiability: The Language of Self-Presentation on a Location-Based Mobile Dating App,” In Proceedings of Mobile HCI 2014, Toronto, Canada, September 23–26. [PDF]
- Blackwell, C., Birnholtz, J., and Abbott, C. (2014) “Seeing and Being Seen: Co-Situation and Impression Formation in a Location-Aware Gay Dating App,” New Media and Society. [LINK]
Face threats on Facebook
We know that Facebook and other online social network sites give us significant power to present positive aspects of ourselves and ensure that others have positive impressions of us. We can post attractive photos from vacations in exotic places, update our statuses with witty, intelligent banter, and share links to fascinating or entertaining content we have discovered. Sometimes, however, our self-presentation on Facebook is controlled by our friends, who may not be as careful in cultivating positive impressions. Friends might post unflattering photos or content, say something in public about embarrassing incidents that happened in private, or post controversial or offensive content that we do not want to be associated with. In this project, we are examining how friends and contacts affect our identity on Facebook, and how people respond to content that is not consistent with their desired self-presentation.
Publications:
- Oledorf-Hirsch, A., Birnholtz, J., and Hancock, J. (2015) “Embarrassed by Friends on Facebook: Effects of and Responses to Face-Threatening Information Shared by Others,” Paper to be presented at the Conference of the International Communication Association (ICA), San Juan, Puerto Rico, May 21–25, 2015.
- Litt, E., Spottswood, E., Birnholtz, J., Hancock, J., Smith, M.E., Reynolds, L. (2014) “Awkward Encounters of an ‘Other’ Kind: Collective Self-Presentation and Face Threat on Facebook,” to appear in Proceedings of the 2014 ACM Conference on Computer-Supported Cooperative Work, Baltimore, MD, February 15-19 [PDF]
- Wohn, D.Y., Birnholtz, J., Hancock, J., Litt, E., and Spottswood, E. (2014) “Impression Curation: Reacting to Other-Generated Face Threats on Facebook,” Presented at the conference of the International Communication Association (ICA), Seattle, WA, May 22–26. [PDF]
Traces and Conflict: Understanding The Value of Ambiguity in Trace Histories
Technologies such as Google Docs and Wave allow for conversation and production of documents. When groups work together, however, some conflict is inevitable. People may be frustrated with others’ behavior or disagree about content authored together. In some cases, we believe technology can also highlight or worsen conflict. Wikipedia, for example, provides detailed trace histories. These logs can draw attention to conflicts that must often be resolved via moderation, and minor edits can enflame tensions if one faction is perceived to be editing more than another. Edit histories, in effect, remove ambiguity about the past; and this can impact the ability to make minor edits without drawing attention, and to smoothly resolve conflicts.
In systems such as Google apps, trace histories are also enabled. While these increase accountability and awareness of the past, they also reduce ambiguity and may constrain the use of certain politeness strategies. There has been little study, however, of how trace histories impact group dynamics.
We will explore ambiguity and trace histories in Google apps, addressing these questions: 1) How are trace histories used to determine what happened in the past?; 2) What ambiguities are introduced/eliminated by trace histories, and how are they used? 3) How are trace histories used in the face of conflict?
Publications
- Birnholtz, J., Steinhardt, S., and Pavese, A. (2013) “Write Here, Write Now!: An Experimental Study of Group Maintenance in Collaborative Writing,” Proceedings of the ACM Conference on Human Factors in Computing Systems (CHI), Paris, France, April 27 – May 2, pp. 961–970. [PDF]
- Birnholtz, J. & Ibara, S. (2012). Tracking changes in collaborative writing: Edits, visibility and group maintenance. Proceedings of the Computer-Supported Cooperative Work Conference (CSCW 2012), February 11-15, 2012, 809-818.
Configurations of Anonymity and Identifiability in Social Networking

Anonymous online interactions allow users the freedom to explore identities and discuss taboo or private topics. However, identified interactions allow verification of others’ expertise and experience, as well as the building of social capital. One reason for the proliferation of modern social networking sites is that each offers a different take on users’ identifiability. Sites such as LinkedIn and Facebook encourage users to create profiles that are highly connected with their offline persona. In other cases, however, there is appeal in anonymity. One example of this is the Facebook confession phenomenon, in which anonymous users submit confessions which are viewed and commented on by identified members of a university or school community. Another example is the site Tumblr, which allows easy switching of personae and the maintenance of multiple blogs. This project explores the appeal of novel configurations of anonymity and identifiability in social networking sites.
Publications:
- Birnholtz, J., Merola, N. A. R., and Paul, A. (2015) “‘Is it Weird to Still Be a Virgin?:’ Anonymous, Locally Targeted Questions on Facebook Confession Boards,” To appear in Proceedings of the ACM Conference on Human Factors in Computing Systems (CHI). Seoul, Korea, April 18–23, 2015. [PDF]
Supporting Interpersonal Awareness in Multicultural Virtual Organizations
When collaborating face-to-face, it’s easy to ask a quick follow-up or clarification question, or get somebody’s help. This is because we can readily see who else is around and whether or not they seem to be available for conversation. In virtual organizations, on the other hand, this can be much more difficult. It’s not obvious who is available and at what time, and sometimes nearly impossible to know if a quick question sent to a collaborator will interfere with another task that he may be working on. These gets even more difficult in cross-cultural collaborations where there can be big differences in acceptable behavior. This project focuses on better understanding how we can more naturally support everyday conversation in virtually organizations, while being sensitive to cultural differences among participants.
Publications
- Bi, N., Birnholtz, J., and Fussell, S. (2014) “Intercultural Awareness: Cultural and Relational Effects on Gathering Awareness Information,” In Proceedings of iConference 2014, Berlin, Germany, March 4–7, pp. 426–443. [PDF]
- Bi, N., Fussell, S., and Birnholtz, J. (2014) “To be like you to be liked by you: Cultural effects on adjusting awareness information gathering behavior,” Proceedings of Collaboration Across Boundaries (CABS), Kyoto, Japan, August 20–22. [PDF]
- Birnholtz, J., Guha, S., Yuan, Y.C., Gay, G., and Heller, C. (2013) “Cross-Campus Collaboration: A Scientometric and Network Case Study of Publication Activity Across Two Campuses of a Single Institution,” Journal of the American Society for Information Science and Technology (JASIST), 64 (1), pp. 162–172. [PDF]
Open Messenger and Attention Management
The objective of this proposal is a theoretical and practical framework for understanding and supporting processes of interpersonal attention management in virtual organizations of geographically distributed individuals. Research on virtual organizations (VOs) – aggregations of individuals, facilities and resources that span geographic and institutional boundaries – is critical because VOs are an increasingly common work structure. They enable interaction between individuals who might not otherwise work together, the sharing of scarce resources, and allow novel ways of solving problems. Despite these advantages, members of VOs often cannot work together as effectively as those who are collocated. One reason for this is the difficulty of opportunistic, informal interactions in VOs. These interactions are critical to troubleshooting and coordination, as when co-workers ask quick questions or respond to others’ requests; exchange information about the task or environment; or make spur-of-the-moment decisions.
While many virtual organizations provide basic communication tools such as instant messaging or video conferencing, members often cannot use these effectively because the tools lack support for the subtlety and nuance of managing one’s availability and attention to others. As a result, many people only sporadically attend to messages from collaborators, or may abandon technologies altogether. One problem limiting research progress in this area is that prior work has not considered attention management as a form of joint action in which both parties act in response to each other.
Publications
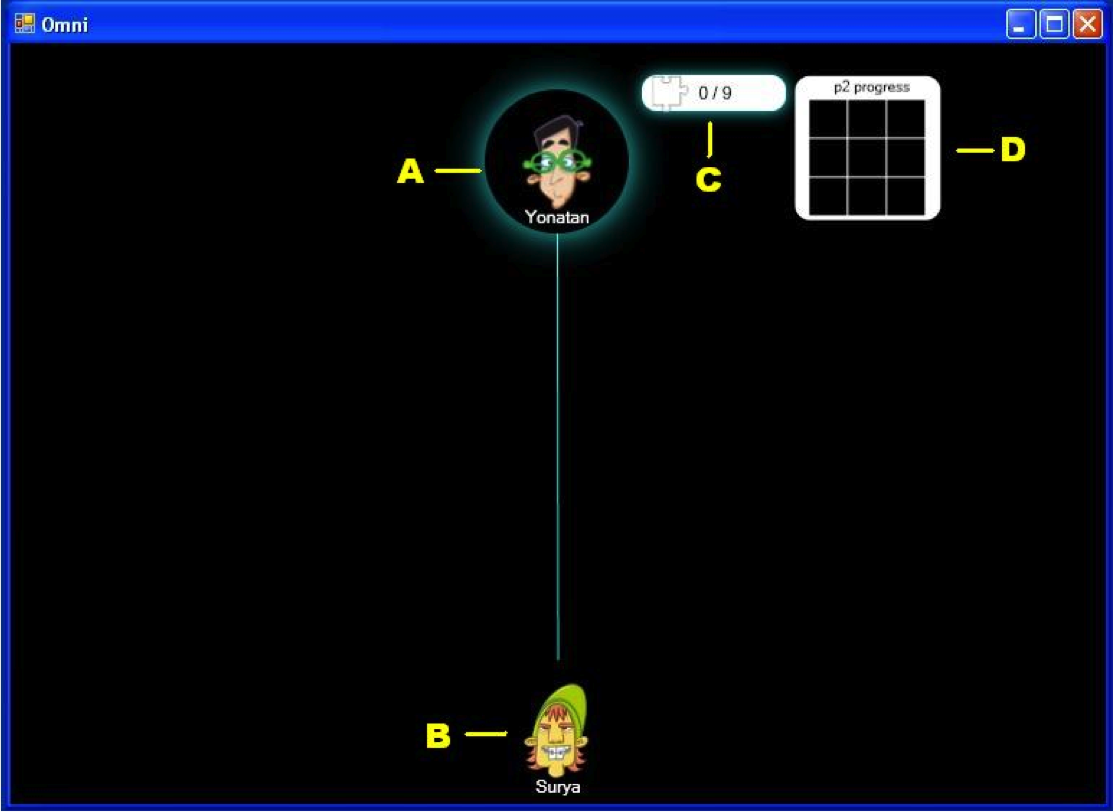
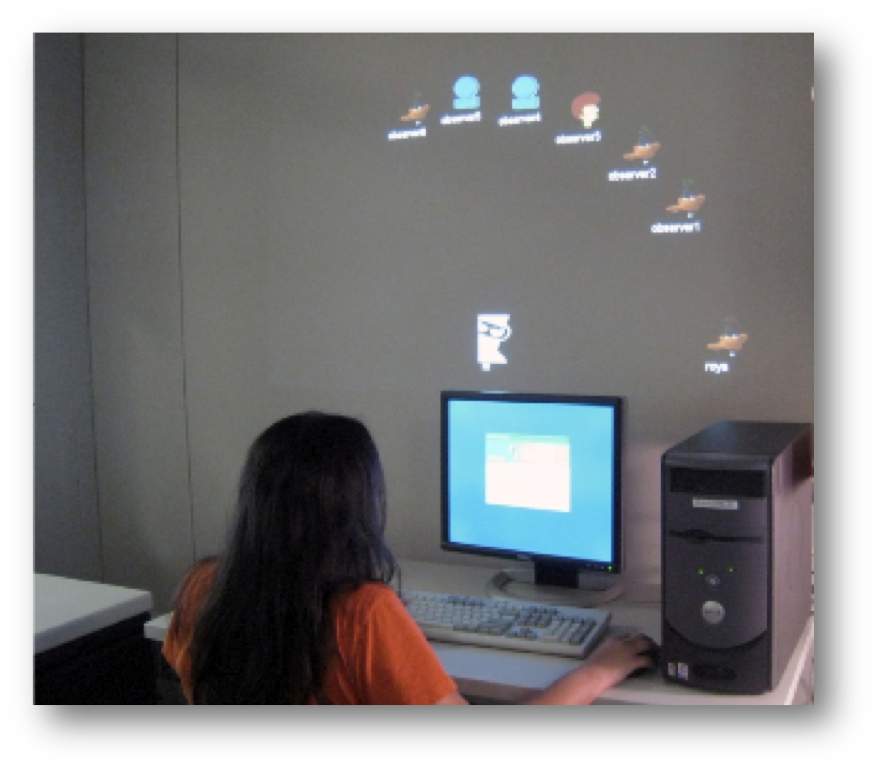
- Birnholtz, J., Bi, N., & Fussell, S. (2012). “Do you see that I see? Effects of perceived visibility on awareness checking behavior. Proceedings of the ACM Conference on Human Factors in Computing Systems (CHI 2012).
- Birnholtz, J., Schultz, J., Lepage, M., & Gutwin, C. (2011). A framework for supporting joint interpersonal attention management in distributed groups. Proceedings of INTERACT, Lisbon, Portugal, September 5-9, 293-312 [Acceptance Rate 27%]